How Tracking Technologies Work, And Why They Violate HIPAA


A quick note before you read: On June 20, 2024, a federal judge vacated a narrow part of the OCR web tracker guidance that an individual’s IP address combined with a visit to a public healthcare website triggered a HIPAA violation. However, the rest of OCR’s web tracking tech guidance remains intact. To keep track of the latest updates, head over to the Freshpaint healthcare privacy hub.
Last year, two class action lawsuits were opened against Meta and more than a dozen were filed against healthcare providers by patients throughout the US. The charge? Violating HIPAA privacy rules and sharing sensitive health information to be used in advertising and marketing.
Last month, GoodRx agreed to a $1.5 million fine for basically the same thing.
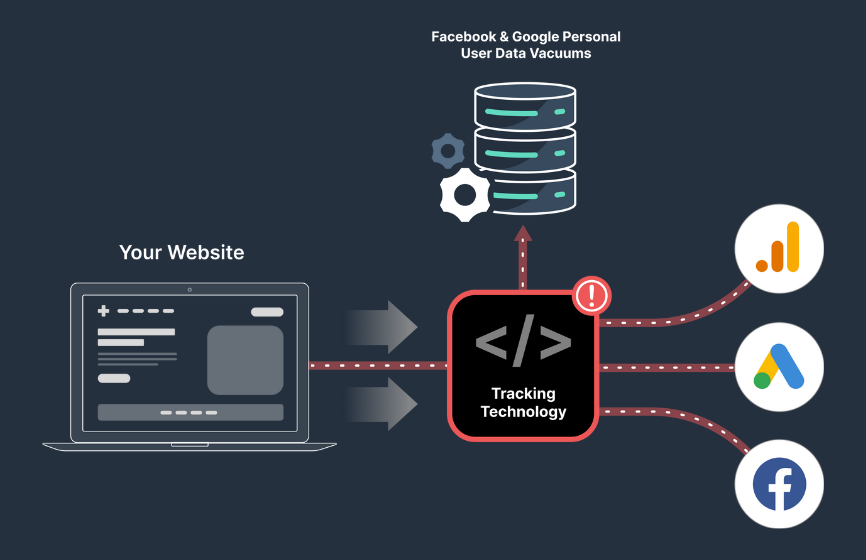
If you’re a healthcare provider using a Meta Pixel or tracking technologies that power Google Analytics or Google Ads, you are in exactly the same position. How these tracking technologies work is fundamentally opposed to privacy. By default, they send identifying information of individual users and health information back to Meta or Google, exactly what the HIPAA privacy rule says you can’t do. In fact, since the Meta imbroglio HIPAA has updated its guidance on tracking technologies to make it explicit how you cannot use these.
So how does this technology work and how is it so incompatible with privacy and healthcare? Let’s go into how companies like Meta and Google track people online. But first a quick primer on PHI so we know what we can’t share about the health of users.
The HIPAA Privacy rule
HIPAA’s privacy rule states:
The Privacy Rule protects all "individually identifiable health information" held or transmitted by a covered entity or its business associate, in any form or media, whether electronic, paper, or oral. The Privacy Rule calls this information "protected health information (PHI)."
"Individually identifiable health information" is information, including demographic data, that relates to:
- the individual's past, present or future physical or mental health or condition,
- the provision of health care to the individual, or
- the past, present, or future payment for the provision of health care to the individual,
and that identifies the individual or for which there is a reasonable basis to believe it can be used to identify the individual. Individually identifiable health information includes many common identifiers (e.g., name, address, birth date, Social Security Number).
That “Individually identifiable” information is important in the context of tracking technologies. There are 18 individual identifiers in the HIPAA guidelines, including “name, address, birth date, Social Security Number,” but also including your IP address, device ID, or ZIP. These are all data points tracking technologies use.
We did a deeper dive in a previous post about what is considered PHI in hopes of ending some of the confusion.
In December, 2022 HIPAA updated guidance to explicitly call out the risk surrounding tracking technologies. They now specifically say:
Regulated entities are not permitted to use tracking technologies in a manner that would result in impermissible disclosures of PHI to tracking technology vendors or any other violations of the HIPAA Rules.
So let’s see how easy it is to “use tracking technologies in a manner that would result in impermissible disclosures of PHI to tracking technology vendors or any other violations of the HIPAA Rules.”
How tracking works
Let’s say you hadn’t heard about all the lawsuits and are going to add a Meta pixel to your site. The first step you’d take is to add this code:
<!-- Facebook Pixel Code -->
<script>
!function(f,b,e,v,n,t,s)
{if(f.fbq)return;n=f.fbq=function(){n.callMethod?
n.callMethod.apply(n,arguments):n.queue.push(arguments)};
if(!f._fbq)f._fbq=n;n.push=n;n.loaded=!0;n.version='2.0';
n.queue=[];t=b.createElement(e);t.async=!0;
t.src=v;s=b.getElementsByTagName(e)[0];
s.parentNode.insertBefore(t,s)}(window, document,'script',
'https://connect.facebook.net/en_US/fbevents.js');
fbq('init', '{your-pixel-id-goes-here}');
fbq('track', 'PageView');
</script>
<noscript>
<img height="1" width="1" style="display:none"
src="https://www.facebook.com/tr?id={your-pixel-id-goes-here}&ev=PageView&noscript=1"/>
</noscript>
<!-- End Facebook Pixel Code -->
So what does this do?
This isn’t the tracking code as such. What this code does is set up the base code for tracking and then load the full tracking code from Meta’s servers asynchronously (so your webpage won’t be slowed down). The full tracking code is within https://connect.facebook.net/en_US/fbevents.js. You can see it’s pretty substantial. All that code is used to track the events on each page.
Why is this called a ‘pixel’? Originally it was just a 1x1 pixel that Facebook would track the loading of on each page and that would be how it would know if the page had been loaded or not. If you look carefully, you can see it still does this as a fallback through the piece of code that reads:
<noscript>
<img height="1" width="1" style="display:none"
src="https://www.facebook.com/tr?id={your-pixel-id-goes-here}&ev=PageView&noscript=1"/>
</noscript>
That is loading a 1x1 pixel. It is in the <noscript> tag as it’s only used if you have JavaScript turned off in the browser.
So you’ve added that code. Sometimes there is also some configuration within the UI on Facebook to decide what you want to track. The way people usually use a Meta pixel is often to track some form of conversion on a page. They can capture information about the person making the conversion using Advanced Matching and either a) target that person with marketing (known as retargeting) or b) feed the data from successful conversions back to Facebook so the ad platform can find similar users who are likely to convert.
To do so, Meta will track information about the user, page and form associated with any conversion (or any non-conversion). Here is what they are capturing and sending:
- HTTP Headers: HTTP Headers include IP addresses, information about the web browser, page location, document, referrer and person using the website.
- Pixel-specific Data: Includes Pixel ID and the Facebook Cookie.
- Button Click Data: Includes any buttons clicked by site visitors, the labels of those buttons and any pages visited as a result of the button clicks.
- Optional Values: Developers and marketers can optionally choose to send additional information about the visit through Custom Data events. Example custom data events are conversion value, page type and more.
- Form Field Names: Includes website field names like email, address, quantity, etc., for when you purchase a product or service. We don't capture field values unless you include them as part of Advanced Matching or optional values.
So let’s think about how this might play out on a healthcare site. You have a “schedule appointment” form on a page that’s being tracked via a Meta pixel. The fields are name, email, date, and doctor. Depending on how you’ve set up Advanced Matching, you might be sending all this information to Facebook. If you are sending all those fields to Meta via the pixel you are definitely sending PHI and in violation of HIPAA.
A way to think about tracking technologies is this: all of the tutorials, guides, and how-tos are for regular web pages with no concern for data privacy. If you are a healthcare company and follow one of these guides, you’re doing it wrong, even though Facebook is telling you you’re doing it right.
Meta has two ‘outs’ here:
- It says if it finds PHI in its data it strips it out and doesn’t use it in any advertising
- It uses a SHA-256 hash to ‘encrypt’ the data.
The problem with (1) is that it is currently being litigated in court whether this is true:
In the complaint, the patient said that Meta harvested sensitive medical information through UCSF and Dignity Health’s patient portals, then sold the data to pharmaceutical and other companies which fed her targeted advertising related to her medical conditions.
This is retargeting. Likely, UCSF and Dignity have tracked the actual form fields on their site (not just the names) and passed these to Meta, who have used them to build up an advertising profile for this user, and then acted upon that information. It’s exactly how adtech tracking is supposed to work, but not in healthcare.
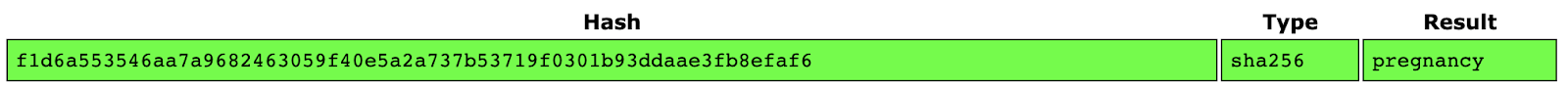
The problem with (2) is that, though SHA-256 hashes are unbreakable, they are also deterministic, meaning that the same plain text will always produce the same encrypted text. So all you need is a long list of plain text with associated encrypted text and you can quickly look up and ‘decrypt’ the code. For instance, if we SHA-256 hash the word ‘pregnancy’ with this tool we get:
F1d6a553546aa7a9682463059f40e5a2a737b53719f0301b93ddaae3fb8efaf6
Which we can decrypt with this tool:
You might think that if you don’t have form data this isn’t a problem. But you are still going to have a problem. First, because it is sending button data by default. This is more of a gray area, but if that button is something like “contact psychiatry,” PHI can easily be inferred.
Second, is the huge problem of those “HTTP headers.” This is the fundamental trap of tracking technologies–they track stuff. Their entire raison d’etre is to track a) a person on b) a page. To do that, they need some way to identify a person, so use the IP address, and a way to identify the page, so use the URL.
The IP address is one of the HIPAA identifiers, and if the tracked page contains health information you have the recipe for what’s prohibited under the HIPAA privacy rule when it comes to tracking technologies.
Here we’ve concentrated on Meta for two reasons:
- They are the ones currently in court
- They have better documented their tracking tools
But Google works pretty much the same way. It is trying to tie an individual to events on a page so that they can build up a profile of that person and serve them ads further down the line.
Using Freshpaint for HIPAA-Compliance
All this would be OK if Meta and Google could be trusted with PHI, but they can’t. In their defense, they know they can’t be trusted–that’s why they won’t sign a BAA.
If you have a Meta pixel, Google Analytics, or Google Ads tracking installed on a healthcare website or product, you must stop sending that data directly to these companies. But you don’t have to abandon the ad platforms or the analytics you use to measure your site’s performance. The simplest path forward is to replace your Facebook and Google tracking technologies with Freshpaint.
Instead of your data going from website -> unsafe tracking technologies -> Facebook/Google, it goes website -> Freshpaint -> Facebook/Google. Doing this allows you to continue using your ad platforms and analytics by taking advantage of Freshpaint’s HIPAA compliant platform.
So, how does Freshpaint keep Facebook Ads, Google Ads, and Google Analytics HIPAA-compliant?
- BAA For Full Protection. Freshpaint signs a BAA and is purpose built to collect, store, and manage sensitive data across your tech stack.
- Safe by Default. Freshpaint’s default state is to never send ANY data to non-compliant tools
- Server-Side Implementation. Unlike tracking technologies that install client-side on a provider’s website, making them vulnerable to intercepting identifiers and health information, Freshpaint is only implemented server-side to give you control over your data.
- Built-in De-Identification. Freshpaint masks user identifiers irreversibly. No downstream analytics tool will have access to raw identifiable information about a user.
- Forced Allowlists. By default, no data is sent to non-compliant destinations such as Google or Facebook Ads. Instead, you choose the data and events you want to continue to send, eliminating the risk of accidentally sending PHI.
Freshpaint’s approach allows you to continue leveraging your ad platforms and analytics tools, but in a HIPAA-compliant way. Meta, Google, and pretty much all tracking technologies just aren’t set up for industries where privacy is essential. If you are running marketing, security, or development of these types of sites, you are in serious jeopardy if you are sending data using those tracking technologies.
Learn more: A Privacy-First Framework for HIPAA Compliance: Managing Third-Party Tracking on Healthcare Websites

.png)
.png)
.png)