Cut the Jargon: A Look at the FTC-HHS Privacy Warning and What It Means For Your Healthcare Org


You might’ve heard that the FTC and the HHS recently joined forces to warn 130 hospital systems and telehealth providers about the HIPAA compliance risks of using web tracking technologies on their websites.
But if not, here’s the gist of it: The FTC and the HHS sent a letter to 130 healthcare organizations alerting them that they might be at risk of violating HIPAA for using common web trackers like Meta’s advertising pixel and Google’s analytics platform.
You can read the full letter here, but the big takeaway is that this letter isn’t just a warning, it’s more of an ultimatum. The letter essentially said to these 130 healthcare orgs, “Stop sharing PHI with third-party platforms or face serious consequences.”
The thing is, these organizations probably don’t even realize they’re sharing PHI with Meta and Google, but it doesn’t matter if they know or not, they’re still doing it.
And what’s more important is that even though this letter was sent to 130 healthcare organizations, it actually serves as a warning to ALL healthcare and healthcare-adjacent companies that are covered by HIPAA.
Why did the FTC and HHS join forces to issue this warning?
Before we get into the warning, let’s pause for a second to talk about why the FTC and HHS joined forces on this.
The HHS generally works to help HIPAA covered entities make sure they protect consumer privacy. But they often don’t get into the “policing” aspect of HIPAA.
That’s where the FTC comes in. They control consumer privacy as a whole, including healthcare, and have more resources available to research and enforce privacy violations. In fact, the FTC just asked for an additional $160M to “investigate and litigate more and increasingly complex matters, such as those involving health privacy.”
This warning falls right in line with that simple explanation. The HHS thinks there are some organizations that might be violating HIPAA through web tracking technologies. The FTC, comes in to play bad cop and lets those organizations know that this is a serious issue that could result in fines and lawsuits.
What did the letter really say?
Okay, back to the task at hand: the letter itself. The most important pieces of this letter are really the first two paragraphs.
Starting with the first paragraph, the joint warning states, “[The OCR and the FTC] are writing to draw your attention to serious privacy and security risks related to the use of online tracking technologies that may be present on your website or mobile application (app) and impermissibly disclosing consumers’ sensitive personal health information to third parties.”
There’s a lot of legalese there, but it’s simply saying, “Hey, we did some research and think there might be some technology on your website that is sharing PHI with non-HIPAA-covered companies.”
At this point, most legal teams at these healthcare orgs are probably thinking, “We’re careful, there’s no chance we’re doing anything wrong here.”
But when we get to the second paragraph, the letter names the companies that these healthcare orgs might be sharing data with. This is the passage that should grab everyone’s attention:
“Recent research, news reports, FTC enforcement actions, and an OCR bulletin have highlighted risks and concerns about the use of technologies, such as the Meta/Facebook pixel and Google Analytics, that can track a user’s online activities.”
That should catch your attention because Meta (aka Facebook) and Google are respectively used by 10’s of millions of websites. Marketers across all industries at companies of all sizes use those tools. That means there’s a good chance that your marketing department is using those tools.
Combined with the first paragraph, the letter is saying, “If you have the Meta (aka Facebook) pixel installed on your website, or if you have Google Analytics installed, there’s a chance you’re violating HIPAA.”
Let’s pause for a second and talk about who is and isn’t covered by HIPAA. Faegre Drinker gave a clear definition in a recent webinar, but to paraphrase:
If you’re a healthcare organization that bills insurance companies, or collects Personal Health Information (PHI)
So, if your organization matches that definition, and you’re using the Meta Pixel or Google Analytics, there’s a non-zero chance that your company is violating HIPAA.
What’s good about this letter is that it still gives healthcare organizations the freedom to choose how to address this problem. In the last paragraph, the joint warning says, “To the extent you are using the tracking technologies described in this letter on your website or app, we strongly encourage you to review the laws cited in this letter and take actions to protect the privacy and security of individuals’ health information.”
That sentence is essentially saying, “We don’t want to tell you how to run your business, but you should find these technologies, and make sure that you’re not sharing PHI with them. If you are, take action to fix the problem. Now.”
How do these tools get PHI when they’re not supposed to?
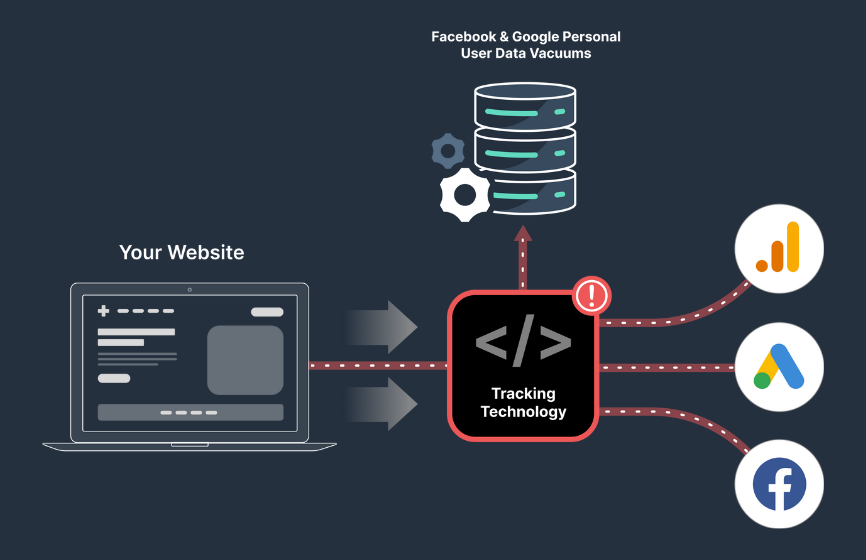
Facebook and Google collect PHI by default because of how they function. Facebook and Google aren’t the only web tracking tools that collect PHI by default, but they are the most commonly used and recognizable so the FTC-HHS warning chose to focus on those two. Plus, they’re the easiest to identify if they’re installed on a website (we’ll show you how in the next section of this article).
Regardless, there are a lot of other tools that can lead to similar HIPAA violations, and it all comes down to how those tools function.
Nearly all website tracking tools (including Facebook/Google), collect the two components of PHI to function:
- Personal Identifiers. This is any data that can reveal the actual identity of an individual. That could be a device ID, email address, or anything else that could point to one specific person visiting a website.
- Health Information. This is the medical information about the user. Something as simple as visiting a find a doctor page or viewing a treatment page with a URL containing fibrolamellar carcinoma would be considered health information.
To drive this point home, let’s use an example. Let’s say you visit the website of FreshHealth, your local healthcare center. They have Google Analytics installed on the website. Google Analytics collects your IP address the second you land on the homepage.
From there, you navigate to a page about treating diabetes and then decide to book an appointment through the website.
Google Analytics now knows your IP address (which is a personal identifier), the URLs you’ve visited (which contain health information), and the actions you’ve taken on FreshHealth’s website during the browsing session (which could also contain health information).

So Google now has both pieces of PHI. And because Google won't sign a BAA for Google Analytics, that’s a clear HIPAA violation.
How do I find out if my website is leaking PHI to one of these tools?
Follow our Privacy-First Framework! Or, if you're short on time, bookmark our Privacy-First Framework and keep reading. Then come back to the Framework when you have more time.
Step 1: Know your tech
First things first, you need to know what tech is running behind the scenes on your website.
The best way to do that is with a tool like Wappalyzer or BuiltWith. These tools can help identify all the technology that is running behind the scenes on your website, including those analytics and tracking tools like Google Analytics and the Meta Pixel.
When you run one of those tools on your website, it’ll put each tool into a specific category. Start by looking at the tools categorized in the analytics and advertising buckets. From there, you’ll also want to look at the marketing automation, personalization, and CRM tools your organization may be using

Despite the fact that the FTC-HHS warning only called out Meta and Google, any of the tools in those categories could also be unknowingly collecting PHI.
Step 2: Do you have a BAA in place?
Once you know what tools you're dealing with, it's time to see if you've got a Business Associate Agreement (BAA) in place with any of those companies. But remember, Meta and Google don't sign BAAs. So if you see those tools from the report in the previous step, you’re at high risk.
If you have a BAA in place, make a note of the tool and move on.
If you don’t have a BAA in place with that tool, find out immediately if they’re willing to sign one. If they are, great. That’s half the battle, but as we wrote in this blog post, there’s still more work to do.
Step 3: No BAA? Dig into what the tools are collecting
If you're working with tools from companies that aren't interested in signing a BAA, you've got some more digging to do. You need to check out what kind of data you're sending to those tools.
Start by looking for personal identifiers. Specifically these 18:
- Name
- Email addresses
- Phone Numbers
- Addresses
- IP Address
- Fax Numbers
- Social security numbers
- Medical record numbers
- Account numbers
- Appointment and Birth Dates
- Any unique identifying number, characteristic, or code
- Vehicle Identification Numbers & License Plates
- Device identifiers and serial numbers
- Web Universal Resource Locators
- Biometric identifiers, including finger and voice prints
- Health plan beneficiary numbers
- Full-face photographs and any comparable images
- Certificate/license numbers
- Geographic Divisions Smaller than a State
Now, finding this information can be done in one of two ways. The first is simple. Log into the platform, see what data is stored there. If you find any of the above identifiers, you’re likely to be in hot water.
If you don’t find any of the above identifiers, you’re actually still not in the clear. There’s a chance that your tracking tech is collecting that information in the background. This is where you need to put on your detective hat and go a level deeper (buckle up, we’re about to get technical)...
Use Google Chrome (it’s the best browser for this detective work) to navigate a condition-specific page or an appointment booking page. We need to see what information is being sent to Google Analytics and/or Facebook on these specific pages because remember, PHI needs two pieces: 1) a personal identifier 2) health information. Health information will be on condition-specific or appointment booking pages.
Now that you’re on one of those pages, right click, and click “Inspect.” This will open up Developer Tools, which is what we’ll use to get an idea of what Google and Facebook are receiving.
Once you’re in Developer Tools, click on “Network” in the top navigation bar.
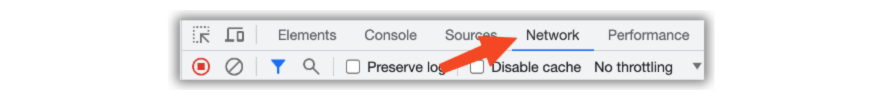
Still with us? Good, let’s keep going.
Once you’re in the Network tab, use the “Filter” bar to type in either:
- analytics.google which will bring up Google Analytics actions
- facebook which will bring up Meta’s pixel actions
Now refresh the entire page.
At this point, you might see some analytics actions appear in Developer Tools. Look specifically for the actions that are categorized as a “ping”. Pings are small packets of data sent to Google Analytics or Facebook.

We’re getting close. Click on the action, which will open up another side bar. At the top of that side bar, click on “Payload.” This will give you an idea of some of the things Google Analytics and/or Facebok are receiving from your website.
From the Payload tab, you’ll see something like this:
- v: 2
- tid: G-DV80NZEZ7E
- gtm: 45je37v0
- _p: 1115432981
- _dbg: 1
- cid: 69273141.1689598566
- ul: en-us
- sr: 1470x956
- uaa: arm
- uab: 64
- uafvl: Not%2FA)Brand;99.0.0.0|Google%20Chrome;115.0.5790.114|Chromium;115.0.5790.114
- uamb: 0
- uam:
- uap: macOS
- uapv: 13.4.0
- uaw: 0
- _s: 1
- sid: 1691074005
- sct: 41
- seg: 1
- dl: https://www.freshpaint.io/blog/what-is-phi-ending-the-confusion
- dr: https://www.google.com/
- dt: What Is PHI? Ending The Confusion
- en: page_view
- _ee: 1
There are a few device and browser identifiers there, but what’s most concerning from a HIPAA point of view is the “cid” – that stands for Client ID, which is how Google Analytics tracks different computers interacting with a website. And, Client ID, falls right into the personal identifier category of “Any unique identifying number, characteristic, or code.”
That could be a HIPAA violation. Yikes.
Step 4: Make a decision
If you find that your site's been sending PHI to third-party tools, you've got to make a decision on how to handle it. You have one of four options:
- Stop using the technology altogether. This can work, but it will leave your marketing team in the dark about performance and cause marketing and advertising costs to increase.
- Build your own. You could, in theory, build your own version of the technology to prevent PHI from being shared with a third party. But the cost and complexity of this option is prohibitive for all but the largest healthcare organizations (and even those often choose not to build their own).
- Find an alternative tool that will sign a BAA. This is a solid option in some instances, but for advertising, it’s not an option because your marketing team needs to reach your audience where they are, which is most likely on one of Facebook’s properties. And, Facebook won’t sign a BAA. Plus, if you go this route, it will force your marketing team to rebuild their analytics plans from scratch. That’s lengthy and confusing.
- Consider using a HIPAA-compliant data intermediary, like Freshpaint, to prevent PHI from getting to those tools. This is the fastest and easiest option. These tools also have a proven track record of helping with HIPAA compliance to help put your legal team at ease.
At the end of the day, patients are expecting two things that almost work against each other: data privacy and an excellent digital experience. Tracking tools enable great digital experiences, but often lack privacy. Most stringent data protection tools lack the ability to provide a great digital experience. Balancing the two is important, and as we said in a recent webinar, HHS guidance leaves room for that balance.
But what if…
At this point, we often hear companies say, “But what if we do X? Does that mean we’re safe from HIPAA violations due to web tracking?”
Let’s take a look at the common reasons companies think they’re safe from this sort of HIPAA violation:
- But what if we use a consent manager? We use one on our website to be GDPR compliant, doesn’t that work for HIPAA? In short, no. Getting consent to collect data through a consent manager doesn’t work for HIPAA. It’s required under other data privacy laws, but HIPAA is more strict than just generally asking for consent to use data.
- But what if a marketing agency built our website and installed those tools? Doesn’t matter. The FTC-HHS letter calls out that exact situation and states that healthcare organizations are still responsible for the tracking technologies on their websites, regardless of who installed them.
- But what if we don’t use the data Facebook/Google collects? Again, it doesn’t matter. It’s still a potential violation because you’re still sharing the data with Facebook and Google, even if you aren’t using it.
- But what if we didn't know we had those tools installed? As with anything else, ignorance is not a reasonable defense. It doesn’t matter who installed the tool or who knows about it. What matters is that it’s there and you’re sharing data with non-compliant tools.
Fortunately, if you find that your organization is using tracking tech and might be leaking PHI to those tools, there are easy ways out. And no, simply removing the tracking tech isn’t the best path forward. Read why here.
A better path forward is using a Healthcare Privacy Platform. Watch the video below to learn how Columbus Regional Health used Freshpaint's Healthcare Privacy Platform to unlock high performance marketing:

.png)

.png)



.jpg)
