What HHS Has to Say About Tracking Technologies in Latest HIPAA Guidance



A quick note before you read: On June 20, 2024, a federal judge vacated a narrow part of the OCR web tracker guidance that an individual’s IP address combined with a visit to a public healthcare website triggered a HIPAA violation. However, the rest of OCR’s web tracking tech guidance remains intact. To keep track of the latest updates, head over to the Freshpaint healthcare privacy hub.
When Microsoft released Internet Explorer 3.0, and President Clinton signed the Health Insurance Portability and Accountability Act (HIPAA) into law in August of 1996, the Internet and healthcare were very different than they are today.
The original language of HIPAA couldn't have anticipated the complexities introduced by the revolutionary changes technology has brought to healthcare. To say we've been overdue for updated guidance from the US Department of Health and Human Services (HHS) is an understatement.
Earlier this month, that guidance finally came. Hot on the heels of class action lawsuits against Facebook's parent company Meta and several large healthcare systems, HHS released HIPAA rules for companies collecting information about how users interact with their websites or apps.
Learn more: A Privacy-First Framework for HIPAA Compliance: Managing Third-Party Tracking on Healthcare Websites
What's the new HHS guidance?
HHS specifically says:
Regulated entities are not permitted to use tracking technologies in a manner that would result in impermissible disclosures of PHI to tracking technology vendors or any other violations of the HIPAA Rules.
It's hard not to make a strong correlation between the high-profile Meta class action lawsuits and the timing of this update. The lawsuits accuse Facebook's Pixel (a tracking technology) of "illegal information gathering." HHS calls explicitly out "tracking technologies" in their guidance.
HHS defines "tracking technologies" as:
Generally, a tracking technology is a script or code on a website or mobile app used to gather information about users as they interact with the website or mobile app. After information is collected through tracking technologies from websites or mobile apps, it is then analyzed by owners of the website or mobile app ("website owner" or "mobile app owner"), or third parties, to create insights about users' online activities. Such insights could be used in beneficial ways to help improve care or the patient experience.
According to HHS:
The HIPAA Rules apply when the information that regulated entities collect through tracking technologies or disclose to tracking technology vendors includes protected health information (PHI).
Capturing customer data to improve product experience, provide more personalized messaging, or improve ad campaigns would all certainly be impacted by this new guidance. Tracking technologies are at the heart of this type of data gathering.
Healthcare providers of all sizes are already telling us the impact these guidelines are having. Many have completely shut off Google Analytics, leaving them in the dark about how users interact with their websites.
HHS states some of the obligations for companies handling PHI through tracking technologies:
- Disclose tracking technologies in the privacy policy or terms.
- You cannot disclose PHI to any vendor without a BAA.
- If you must disclose PHI to a non-compliant vendor, you must first have authorization from the individual.
Google and Facebook refuse to sign BAAs, so their tracking technologies are in clear violation of HIPAA.
Let's cover two scenarios to see the new guidance's specific impacts on healthcare companies.
Situation 1: I have a public website that gives information about conditions and allows users to connect with a medical professional
The Google and Facebook pixels capture a lot of information about the users visiting your websites. Things like IP address would automatically trigger a violation of HIPAA if it's linked to PHI.
Here's the language from the HHS guidance:
Individually identifiable health information (IIHI)] might include an individual's medical record number, home or email address, or dates of appointments, as well as an individual's IP address or geographic location, medical device IDs, or any unique identifying code. All such IIHI collected on a regulated entity's website or mobile app generally is PHI, even if the individual does not have an existing relationship with the regulated entity and even if the IIHI, such as IP address or geographic location, does not include specific treatment or billing information like dates and types of health care services.
Some specific examples where companies might get tripped up:
- If your public website contains a page where users can sign up for or login to an account (users typically enter their email or a user ID)
- If your public website contains a doctor lookup that allows users to filter by specific condition (IP address and condition now linked)
- If your public website has a page where users can book an appointment.
Most providers we've talked to are using tracking technologies to power Google Analytics and potentially Facebook and Google Ads. All of those tracking technologies are putting them at risk.
Situation 2: I have an app where patients book appointments, have telehealth visits and receive test results
This one is straightforward. Almost everything done in this app – from the login, appointment, conditions, and IP address is PHI and covered by HIPAA rules.
As the complexity of your tech stack scales in supporting an app like this, so do the number of tracking tools required to maintain it. Many health tech companies end up with multiple destinations for their customer data. Your tech stack might look something like this:
- Product analytics tools (many use Google Analytics at early stages and then graduate to Mixpanel, Amplitude, or similar)
- Session replay tools (CrazyEgg, HotJar)
- Chat tools (Drift, Intercom)
- Support tools (Freshdesk, Zendesk)
- Messaging tools (Iterable, Intercom)
- CDPs (Freshpaint, Segment)
- Ad platforms (Facebook, Google)
These tools are used extensively to help tech companies provide a better user experience and leverage user interactions with their application. All of these tools can inject PHI and, without the correct setup, could cause violations of HIPAA.
With HHS's new guidance, it's critical to have BAAs signed for destinations that will handle PHI. Remember that some platforms like Facebook, Google, and Hubspot won't even sign a BAA. Other tools charge extra for a signed BAA. To prevent inadvertently sharing PHI where you don't have a BAA, you'll need to invest in putting workflows in place.
What should I do now?
Here are some things you should talk about with your team.
- What tracking technologies do we have in place?
- What tools need PHI to perform their function (like emailing appointment reminders)?
- Do we have a BAA in place with all of them?
- What tools don't need PHI to perform their function?
- How do we guarantee that PHI is never shared with those tools?
- Part of HHS's guidance is to minimize the amount of PHI captured by tracking tools.
- What do our vendors do beyond simply signing a BAA to protect PHI?
How can Freshpaint help?
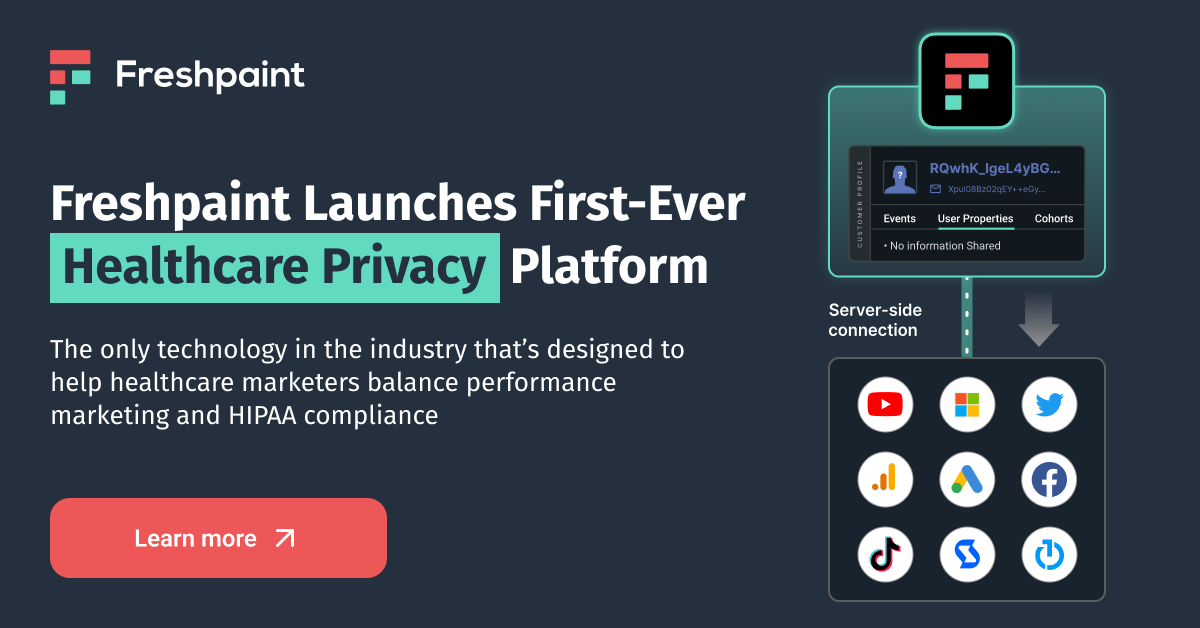
Freshpaint's Healthcare Privacy Platform is purpose-built for healthcare and is HIPAA-compliant by default, whereas generic CDPs are not. What does this mean?
Bottom line is that Freshpaint can make tools like Google Analytics HIPAA compliant, so providers don't need to find a new solution.
Let's dive in to understand more about how we do that.
Default hashing of user identifiers
- By default, Freshpaint irreversibly hashes user identifiers. This allows you to safely send data to destinations that are not HIPAA compliant, so you can still track that user's behavior without revealing the user's identity.
- Generic CDPs require custom engineering work to create a unique user identifier whenever you want to send data to a new destination. One customer told us this would cost a full-time engineer to manage it.
Separate HIPAA compliant from non-compliant destinations
- Your warehouse and engagement platform (like Iterable and Customer.io) are typically HIPAA-compliant. You’ll need to send PHI so they can fully function.
- Send safely to non-compliant destinations (Google, Facebook, and Hubspot won't even sign BAAs). User identities will be hashed and PHI will be blocked by Freshpaint.
- Product analytics tools use data in aggregate, so you generally don't need a BAA when using Freshpaint - saving money on additional BAA-related costs.
Freshpaint blocks data from going to non-compliant destinations by default
- Freshpaint is safe by default. You must choose which data is safe to send to downstream destinations. This eliminates the risk of accidentally sending PHI and violating HIPAA.
- Generic CDPs send all the data to the destination by default. You have to select what not to send. This causes inadvertent leaks of PHI, like sensitive info in a URL name or an IP address.
Learn how Columbus Regional Health navigated the complexities of this guidance with the help of Freshpaint:

.png)
.png)



.jpg)
