Cookie Consent Tools: The Big Legal Blind Spot in Healthcare Marketing



Every day in healthcare marketing, legal, and compliance circles, a dangerous assumption is quietly taking root: “We have a cookie banner, so we’re covered.”
It’s an assumption that feels safe. It’s convenient. And it’s dead wrong.
If you think a cookie banner or even a full consent management platform (CMP) is the only shield you need to comply with the complex web of privacy laws in the U.S., you’re not just misinformed—you may be actively walking your organization into a multimillion-dollar compliance disaster.
The first step to remedying this situation is to understand what consent management platforms (CMPs) actually do… and don’t do.
The Cookie Consent Reality Check
First, let’s be clear about terms used interchangeably throughout the industry:
- Cookie Banner: Just the pop-up notification you see ("This site uses cookies")—it's a message, not a control mechanism.
- Cookie Preferences or Preference Center: The interface where users choose which cookie categories to allow (necessary, functional, analytics, marketing)—these are the settings, not the enforcement.
- Consent Management Platform (CMP): The full technical system that's supposed to display banners, collect preferences through preference centers, AND actually block or allow scripts based on those choices.
For the rest of this article, when we talk about the limitations of consent tools, we're talking about full CMPs—not just banners. Because CMPs are sometimes marketed as a fix-all for data privacy obligations. They pop up, ask users for consent, store the preference, and even let you feel like you’ve checked the “compliance” box.
But here’s the truth most vendor splash pages don’t tell you: Most CMPs don’t actually stop data from leaving your site—they record preferences. And unless you’ve configured and verified your data layer to enforce those preferences, trackers can (and often do) still fire.
Pixels, session replay scripts, analytics SDKs, and other data-hungry technologies often load before consent is even processed—sometimes in ways your CMP can’t even detect. And the regulators have shown they don’t care if the sharing was “accidental” or “unintentional.”
What CMPs Actually Do—and Don’t Do
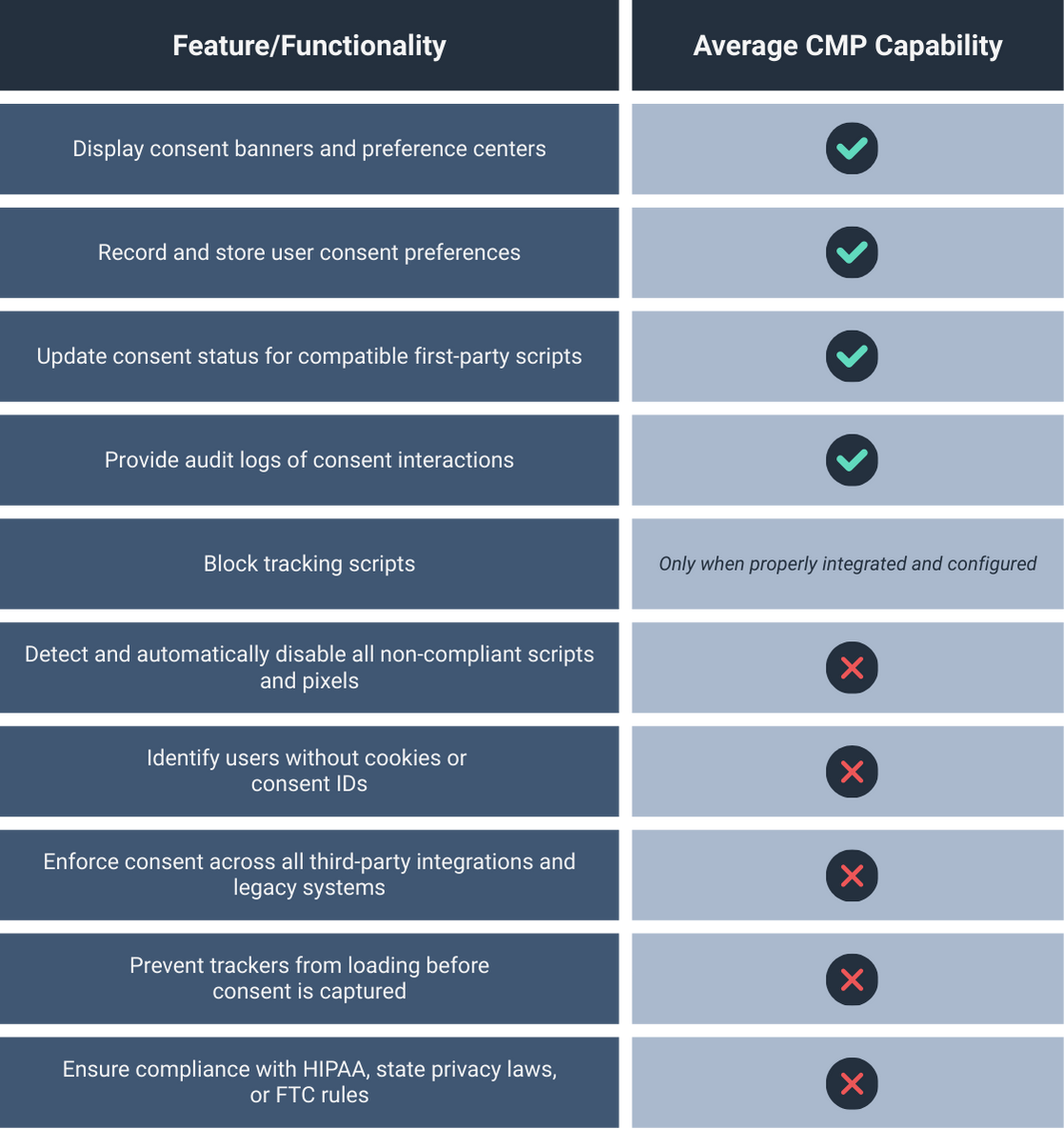
And that’s the trap. On paper, CMPs check some important boxes. But when you zoom out to the full regulatory picture, those checked boxes can barely scratch the surface of what’s required.
Why does this matter? Well…
A Nationwide Privacy Lawsuit Storm is Brewing
Now let’s pull back the curtain on the complex web of privacy laws in the U.S.—the overlapping federal and state rules that don’t just coexist, but often stack penalties on top of each other.
Forget memorizing acronyms. What matters is understanding the operational risks that actually trip organizations up—and the statutes that turn those mistakes into enforcement actions. Each of these risk areas has multiple laws behind it, and more states joining the party every quarter.
1. Consent and Opt-Out Enforcement
The gist of the risk: Trackers can still fire despite a user’s opt-out—whether from a cookie banner click, a preference center setting, or a Global Privacy Control (GPC) signal.
Relevant laws:
- CPRA/CCPA (California): Sale/sharing opt-outs, GPC recognition, contract rules for service providers.
- NYCPA (New York): Explicit consent for sensitive data, opt-out rights, data minimization.
- Colorado, Connecticut, Virginia, Utah, Texas, Oregon: Similar opt-out and sensitive data rules.
Why CMPs fall short: CMPs record preferences but often can’t guarantee trackers stop firing. Any delay, misconfiguration, or non-compatible script can turn into a per-violation penalty.
What compliance looks like:
- Block-by-default until consent is confirmed.
- Honor GPC signals across all trackers.
- Service provider contracts that mirror opt-out obligations.
2. Unauthorized Health-Data Collection and Sharing
The gist of the risk: Health or health-adjacent data leaves your site without the explicit authorization the law demands.
Relevant laws:
- HIPAA (federal): Using or disclosing PHI requires specific patient authorization unless an exception applies.
- MHMDA (Washington): “Consumer health data” is broadly defined; explicit consent is required for its collection, sharing, and sale.
- HBNR (FTC): Disclosing non-HIPAA health records without consent can trigger breach-style notification rules.
Why CMPs fall short: A consent manager alone doesn’t meet HIPAA’s or MHMDA’s consent standards. Trackers can transmit health data before consent is captured, creating instant violations.
More importantly, even with “consent,” PHI cannot be sent to any vendor that hasn’t signed a BAA. Period.
What compliance looks like:
- PHI suppression at the data layer.
- Consent gating that meets HIPAA and MHMDA standards.
- Business Associate Agreements (BAAs) with all relevant vendors.
3. Interception and Surveillance of User Communication
The gist of the risk: Session replay scripts, chat monitoring, or pixels capture keystrokes, clicks, or form data without valid prior consent.
Relevant laws:
- CIPA (California) and similar state “wiretap” statutes: Prohibit interception without prior, specific consent.
Why CMPs fall short: Clicking “Accept Cookies” after the data has already been shared is not considered effective “prior consent” to intercept. Most CMPs run after initial scripts fire—meaning interception may already have occurred.
What good looks like:
- Route-based blocking to prevent replay/pixel scripts from loading on sensitive pages.
- No interception tools running before explicit consent is captured.
4. Deception, UDAP, and Breach Exposure
The gist of the risk: Disclosures don’t match what’s actually happening with user data, or unauthorized data sharing triggers notification duties.
Relevant laws:
- FTC Act and state Unfair and Deceptive Acts and Practices statutes (UDAP): Prohibit deceptive or unfair trade practices; applies to omissions, vague language, dark patterns, and “consent theater.”
- HBNR: Requires consumer, FTC, and sometimes media notification when certain health data is breached.
Why CMPs fall short: Publishing banners with text that contradicts actual tracking behaviors can be considered an unfair and deceptive practice.
What good looks like:
- Disclosures written in plain language that match actual practices.
- Purpose limitations baked into data flows.
- Breach triggers mapped and monitored.
Other states are coming fast, too
Even if you’ve never touched a California or Washington patient or consumer, similar requirements are active or pending in CO, CT, VA, UT, TX, OR—with more to follow. Many define “sensitive data” to include health-adjacent data like an individual’s geolocation if near a clinic, appointment scheduling flows, and diagnosis or symptom-specific content, and can carry AG enforcement penalties in the $5,000–$7,500 range per violation.
This isn’t a gentle drizzle of regulation you can wait out under an umbrella. It’s a coast-to-coast front, and the forecast calls for overlapping laws, conflicting requirements, and penalties that stack like bad Jenga moves. One tracking misfire? You could end up answering to three regulators before lunch.
Beyond Consent (What True Compliance Looks Like)
Let’s be clear: CMPs have their place. But they’re not lifeboats. They’re the laminated safety card in the seat-back pocket—a thing you read while the water is already rushing in.
Without enforcement at the data layer, a CMP alone is just a polite tap on the user’s shoulder while trackers slip out the back door with their data. Think: a “No Trespassing” sign… in neon… above an open gate.
And regulators don’t care if your banner is beautiful, or if your preferences page has drop shadows and rounded corners. They care if you stopped the data from leaking in the first place.
Legitimate compliance in this climate requires going beyond consent to actively enforce data governance rules:
- Blocking unauthorized trackers before they load.
- Stripping/anonymizing sensitive data using methods that comply with laws and regulations before it leaves your systems.
- Integrating only with vendors who meet HIPAA and state privacy law requirements.
- Auditing data flows continuously to catch new risks.
This is the work CMPs don’t always do.
So if you continue to rely solely on a cookie banner or even a traditional CMP to protect your organization, you’re betting your business on a dangerous myth. And in healthcare, the cost of being wrong isn’t just a fine—it’s the trust of the people you serve.
Freshpaint exists to help you close the gap between what you think is happening and what’s actually happening with your data—and to ensure your compliance strategy is more than a banner.
Stop assuming you’re covered. Start verifying that you are. Contact us today.

.png)





.jpg)
